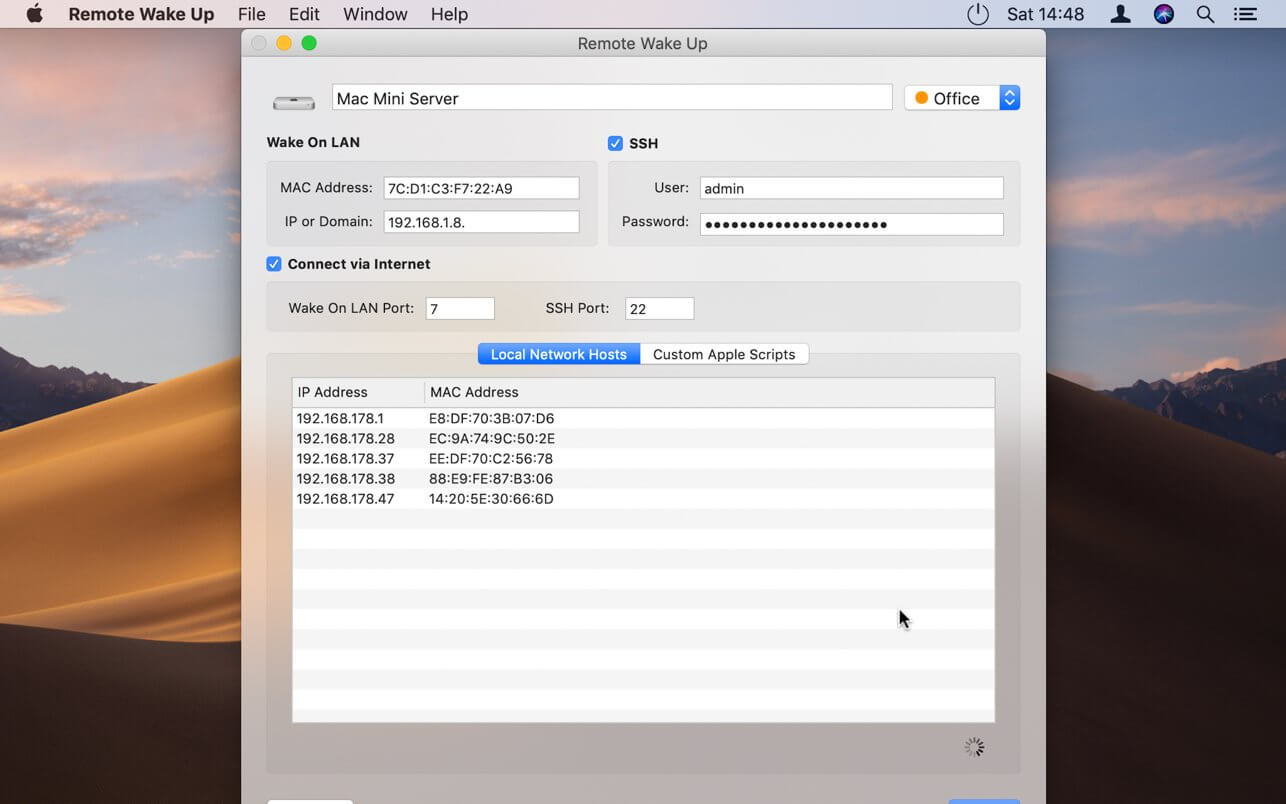
The 3-pin WoL interface on the motherboard consist of pin-1 +5V DC (red), pin-2 Ground (black), pin-3 Wake signal (green or yellow). By supplying the pin-3 wake signal with +5V DC the computer will be triggered to power up provided WoL is enabled in the BIOS configuration. I have got suspend working but the wake is only via the keyboard not IR Remote or mouse. I have read up on a range of forums to find the answer and tried a number of. Jan 03, 2014 Remote Wake Up 1 3 14 Full. From the list of all your connected networks, right click on the network you are using currently. Click on Status. On a General tab of your LAN, tap on Details. Here you can see all your current Physical address of PC, IPv4 address. Take a screenshot of this. Remote Wake Up is a tool that allows you to remotely switch on every Wake On Lan capable device. You can also wake up devices over the internet. Additionally Remote Wake Up allows you to reboot, shut down, send other Macs to sleep or even send AppleScripts using SSH.
-->System configuration, reset control, local wake-up, remote wake-up, undervoltage detection and configuration control. A number of power-supply-related functional blocks are defined: an internal 1.8 V regulator for the digital core, a Very Low Power (VLP) supply for Sleep mode, the reset circuit, supply monitoring and inhibit control.
This topic describes best practices about implementing the remote wakeup capability in a client driver.
USB devices that can respond to external wake signals while suspended are said to have a remote wakeup capability. Examples of devices that have a remote wakeup capability are mice, keyboards, USB hubs, modems (wake on ring), NICs, wake on cable insertion. All of these devices are capable of producing remote wake signaling. Devices that are not capable of generating remote wake signaling include video cameras, mass storage devices, audio devices, and printers.
Drivers for devices that support remote wakeup signaling must issue an IRP_MN_WAIT_WAKE IRP, also known as a wait wake IRP, to arm the device for remote wakeup. The wait wake mechanism is described in the section Supporting Devices That Have Wake-Up Capabilities.
When Does the System Enable Remote Wakeup on a USB Leaf Device?
In USB terminology, a USB device is enabled for remote wakeup when its DEVICE_REMOTE_WAKEUP feature is set. The USB specification specifies that host software must set the remote wakeup feature on a device 'only just prior' to putting the device to sleep.
For this reason, the USB stack does not set the DEVICE_REMOTE_WAKEUP feature on a device after receiving a wait wake IRP for the device. Instead, it waits until it receives a IRP_MN_SET_POWER request to change the WDM device state of the device to D1/D2. Under most circumstances, when the USB stack receives this request, it both sets the remote wakeup feature on the device and puts the device to sleep by suspending the device's upstream port. When you design and debug your driver, you should keep in mind that there is a loose relationship between arming a USB device for wakeup in software, by means of a wait wake IRP, and arming the device for wakeup in hardware by setting the remote wakeup feature.
The USB stack does not enable the device for remote wakeup when it receives a request to change the device to a sleep state of D3, because according to the WDM power model, devices in D3 cannot wake the system.
Why Does Attaching or Detaching My Device Produce a Different Wakeup Behavior in Windows XP and Windows Vista and later versions of Windows?
Another unique aspect of the USB implementation of the WDM power mode regards the arming of USB hubs for remote wakeup. In Microsoft Windows XP all hub devices between host controller and the USB device are armed for wakeup whenever the USB device is armed for wakeup. This produces the surprising consequence that when sleeping devices are detached they will wake up the system.
In Windows Vista and later versions of Windows, if a USB leaf device on the bus is armed for wake, the USB stack will also arm the USB host controller for wake, but it will not necessarily arm any of the USB hubs upstream of the device. The USB hub driver arms a hub for remote wakeup only if the USB stack is configured to wake up the system on attach and detach (plug/unplug) events.
Note UHCI (Universal Host Controller Interface) USB host controllers do not distinguish between remote wake signaling and connect change events on root hub ports. This means the system will always wake from a low system power state if a USB device is connected to or disconnected from a root hub port, if there is at least one device behind the UHCI controller that is armed for wake.
Related topics
Article Copyright Wikipedia - Back to Knowledge Base
Wake-on-LAN (WOL) is an Ethernet computer networking standard that allows a computer to be turned on or woken up by a network message.
The message is usually sent by a program executed on another computer on the same local area network. It is also possible to initiate the message from another network by using Subnet directed broadcasts or a WOL gateway service. Equivalent terms include wake on WAN, remote wake-up, power on by LAN, power up by LAN, resume by LAN, resume on LAN and wake up on LAN. In case the computer being woken is communicating via Wi-Fi, a supplementary standard called Wake on Wireless LAN (WoWLAN) must be employed.[1]
The WOL and WoWLAN standards are often supplemented by vendors to provide protocol-transparent on-demand services, for example in the Apple Bonjour wake-on-demand (Sleep Proxy) feature.[2]
History
In October 1996, Intel and IBM formed the Advanced Manageability Alliance (AMA). In April 1997, this alliance introduced the Wake-on-LAN technology.[3][4]
The term 'Wake on LAN' is a trademark of IBM Corporation.[5]
Principle of operation
Wake-on-LAN is implemented using a special network message called a magic packet. The magic packet contains the MAC address of the destination computer. The listening computer waits for a magic packet addressed to it and then initiates system wake-up.
Simlab composer 7 1 1 download free. The magic packet is sent on the data link or layer 2 in the OSI model and broadcast to all NICs using the network broadcast address; the IP-address (layer 3 in the OSI model) is not used.
It is a common misconception that because Wake-on-LAN is built upon broadcast technology it can only be used within the current network subnet. While this is generally the case there are some exceptions.
In order for Wake-on-LAN to work, parts of the network interface need to stay on. This consumes standby power, much less than normal operating power. If Wake-on-LAN is not needed, disabling it may reduce power consumption slightly while the computer is switched off but still plugged in.[6]
Magic packet
The magic packet is a broadcast frame containing anywhere within its payload 6 bytes of all 255 (FF FF FF FF FF FF in hexadecimal), followed by sixteen repetitions of the target computer's 48-bit MAC address, for a total of 102 bytes.
Since the magic packet is only scanned for the string above, and not actually parsed by a full protocol stack, it may be sent as any network- and transport-layer protocol, although it is typically sent as a UDP datagram to port 7 or 9, or directly over Ethernet as EtherType 0x0842.[7]
A standard magic packet has the following basic limitations:
- Requires destination computer MAC address (also may require a SecureOn password)
- Does not provide a delivery confirmation
- May not work outside of the local network
- Requires hardware support of Wake-On-LAN on destination computer
The Wake-on-LAN implementation is designed to be very simple and to be quickly processed by the circuitry present on the network interface card (NIC) with minimal power requirement. Because Wake-on-LAN operates below the IP protocol layer the MAC address is required and makes IP addresses and DNS names meaningless.
Subnet directed broadcasts
A principal limitation of standard broadcast Wake-On-LAN is that broadcast packets are generally not routed. This prevents the technique being used in larger networks or over the internet. Subnet Directed Broadcasts (SDB)[8][9] may be used to overcome this limitation. SDB may require changes to intermediate router configuration. Subnet directed broadcasts are treated as normal network packets until processed by the final (local) router. This router converts the packet into a true broadcast packet. This technique allows a broadcast to be initiated on a remote network but requires all intervening routers to forward the SDB.[10][11] When preparing a network to forward SDB packets, care must be taken to filter such that only desired (e.g. WoL) SDB packets are permitted—otherwise the network becomes a participant in DDoS attacks such as the Smurf Attack.
Troubleshooting magic packets
Wake-on-LAN can be a frustrating technology to implement. This is because it requires appropriate BIOS, network card and, sometimes, operating system and router support to function reliably. In some cases, hardware may wake from one low power state but not from others. This means that due to hardware issues the computer may be waking up from the 'fully off state' (S5) but doesn't wake from sleep or hibernation or vice-versa. Also, it is not always clear what kind of magic packet a NIC expects to see.
In that case, software tools like a packet analyzer can help with Wake-on-LAN troubleshooting as they allow to confirm (while the PC is still on) that the magic packet is indeed seen by a particular computer's NIC. The same magic packet can then be used to find out if the computer powers up from an offline state. This allows networking issues to be isolated from other hardware issues. In some cases they also confirm that the packet was destined for a specific PC or sent to a broadcast address and they can additionally show the packet's internals.
In Windows Vista and higher, one can also determine how the OS was powered up. Running the powercfg /lastwake command in a CMD prompt will list the 'Wake Source'. The Wake-on-LAN event should also be logged in the System event log.[12]
Security Considerations
Unauthorized access
Magic packets are sent via the data link or OSI-2 layer, which can be used or abused by anyone on the same LAN, unless the L2 LAN equipment is capable of (and configured for) filtering such traffic to match site-wide security requirements.
Firewalls may be used to prevent clients among the public WAN from accessing the broadcast addresses of inside LAN segments, or routers may be configured to ignore subnet-directed broadcasts (see above.)
Certain NICs support a security feature called 'SecureOn'. It allows users to store within the NIC a hexadecimal password of 6 bytes. Clients have to append this password to the magic packet. The NIC wakes the system only if the MAC address and password are correct. This security measure significantly decreases the risk of successful brute force attacks, by increasing the search space by 48 bits (6 bytes), up to 296 combinations if the MAC address is entirely unknown. However any network eavesdropping will expose the cleartext password.
Still, only a few NIC and router manufacturers support such security features.[citation needed]
Abuse of the Wake-on-LAN feature only allows computers to be switched on; it does not in itself bypass password and other forms of security.
Interactions with network access control
The use of Wake-on-LAN technology on enterprise networks can sometimes conflict with network access control solutions such as 802.1x or MAC-based authentication, which may prevent magic packet delivery if a machine's WoL hardware has not been designed to maintain a live authentication session while in a sleep state.[13] Configuration of these two features in tandem often requires tuning of timing parameters and thorough testing.
Data privacy
Some PCs include technology built into the chipset to improve security for Wake-on-LAN. For example, Intel AMT (a component of Intel vPro technology), includes Transport Layer Security (TLS), an industry-standard protocol that strengthens encryption.[14]
AMT uses TLS encryption to secure an out-of-band communication tunnel to an AMT-based PC for remote management commands such as Wake-on-LAN. AMT secures the communication tunnel with Advanced Encryption Standard (AES) 128-bit encryption and RSA keys with modulus lengths of 2,048 bits.[15][16] Because the encrypted communication is out-of-band, the PC's hardware and firmware receive the magic packet before network traffic reaches the software stack for the operating system (OS). Since the encrypted communication occurs 'below' the OS level, it is less vulnerable to attacks by viruses, worms, and other threats that typically target the OS level.[14]
IT shops using Wake-on-LAN through the Intel AMT implementation can wake an AMT PC over network environments that require TLS-based security, such as IEEE 802.1x, Cisco Self Defending Network (SDN), and Microsoft Network Access Protection (NAP) environments.[14] The Intel implementation also works for wireless networks.[14]
Hardware Requirements
Wake-on-LAN support is implemented on the motherboard (BIOS) of a computer and the network interface (firmware), and is consequently not dependent on the operating system (and NIC drivers) running on the hardware. Some operating systems can control Wake-on-LAN behaviour via hardware drivers. If the network interface is a plug-in card rather than being integrated into the motherboard, the card may need to be connected to the motherboard by an additional cable. Motherboards with an embedded Ethernet controller which supports Wake-on-LAN do not need a cable. The power supply must meet ATX 2.01 specifications.
Hardware implementations
Older motherboards must have a WAKEUP-LINK header onboard connected to the network card via a special 3-pin cable; however, systems supporting the PCI 2.2 standard and with a PCI 2.2 compliant network adapter card do not usually require a Wake-on-LAN cable as the required standby power is relayed through the PCI bus.
PCI version 2.2 supports PME (Power Management Events). PCI cards send and receive PME signals via the PCI socket directly, without the need for a Wake-on-LAN cable.[17]
Wake-on-LAN usually needs to be enabled in the Power Management section of a PC motherboard's BIOS setup utility, although on some systems, such as Apple computers, it is enabled by default. On older systems the bios setting may be referred to as 'WOL', on newer systems supporting PCI version 2.2, it may be referred to as 'PME' (Power Management Events, which include WOL). It may also be necessary to configure the computer to reserve standby power for the network card when the system is shut down.
In addition, in order to get Wake-on-LAN to work it is sometimes required to enable this feature on the network interface card or on-board silicon. Details of how to do this depend upon the operating system and the device driver.
Sticker 1 0 3 – organize your windows. Laptops powered by the Intel Centrino Processor Technology or newer[18] (with explicit BIOS support) allow waking up the machine using wireless Wake on Wireless LAN (WoWLAN).
In most modern PCs, ACPI is notified of the 'waking up' and take control of the Power up. In ACPI, OSPM must record the 'wake source' or the device that is causing the power-up. The device being the 'Soft' power switch, the NIC (via Wake-on-LAN), the cover being opened, a temperature change, etc.[12]
The 3-pin WOL interface on the motherboard consist of pin-1 +5V DC (red), pin-2 Ground (black), pin-3 Wake signal (green or yellow).[19] By supplying +5V DC to the pin-3 wake signal with +5V DC the computer will be triggered to power up provided WOL is enabled in the BIOS configuration.
Software Requirements
Software which sends a WoL magic packet is referred to in different circles as both a 'client' and a 'server', which can be a source of confusion. While WoL hardware/firmware is arguably performing the role of a 'server', web based interfaces which act as a gateway through which users can issue WoL packets without downloading a local client often become known as 'The Wake On LAN Server' to users. Additionally, software that administers WoL capabilities from the host OS side may be carelessly referred to as a 'client' on occasion, and of course, machines running WoL generally tend to be end-user desktops, and as such, are 'clients' in modern IT parlance.
Sending the magic packet
1/3 As A Percent
Software to send WoL magic packets is available for all modern platforms, including Windows, Macintosh and Linux, plus many smart phones. Also there are web sites on the Internet that allow a magic packet to be sent online without charge. Example source code for a developer to add Wake-on-LAN to a program is readily available in many computer languages.[20][21][22][23]
Some home routers are able to send magic packets to LAN, for example routers with the DD-WRT or Tomato firmware have a built-in Wake On Lan client. The 3rd party FOSS project OpenWrt supports both Linux implementations for WoL etherwake and wol.
Receiving the magic packet
Most WoL hardware may be configured directly using the system BIOS. However, it is often more desirable to configure the functionality without interrupting the normal operations of the machine. The BIOS step is necessary in addition to configuration from the OS in some cases.
Microsoft Windows
Modern versions of Microsoft Windows integrate WoL functionality into the Device Manager. This is available in the Power Management tab of each network device. In most cases correct BIOS configuration is also required for WoL to function.
Remote Wake Up 1 3 1997 Chevy Truck
Mac hardware (OS X)
Modern Mac hardware features integrated WoL functionality, controlled via the OS X System Preferences Energy Saver panel, in the Options tab. Marking the Wake for network access checkbox enables Wake-on-LAN.
Apple's Apple Remote Desktop client management system can be used to send Wake-on-LAN packets, but there are also freeware and shareware Mac OS X applications available.
On Mac OS X Snow Leopard, the service is called Wake On Demand or Bonjour Sleep Proxy and is synonymous with the Sleep Proxy Service. It comes enabled out of the box, but for previous versions of the operating system, the service will need to be enabled under the Energy Saver pane of System Preferences. The network interface card may allow the service to function only on WiFi, only on Ethernet, or both.[24]
Linux
Wake-on-LAN support may be changed using a subfunction of the ethtool command.
Other Machine States and LAN Wakeup Signals
In the early days of Wake-on-LAN the situation was relatively simple: a machine was connected to power but switched off, and it was arranged that a special packet be sent to switch the machine on.
Since then many options have been added and standards agreed upon. A machine can be in 7 power states from S0 (fully on) through S5 (powered down but plugged in) and disconnected from power (G3, Mechanical Off), with names such as 'sleep', 'standby', and 'hibernate'. In some reduced-power modes the system state is stored in RAM and the machine can wake up very quickly; in others the state is saved to disk and the motherboard powered down, taking at least several seconds to awake. The machine can be woken from a reduced-power state by a variety of signals.
The machine's BIOS must be set to allow Wake-on-LAN. To allow wakeup from powered-down state S5, wakeup on PME (Power Management Event) is also required. The Intel adapter allows 'Wake on Directed Packet', 'Wake on Magic Packet', 'Wake on Magic Packet from power off state', and 'Wake on Link'.[25] Wake on Directed Packet is particularly useful as the machine will automatically come out of standby or hibernation when it is referenced, without the user or application needing to explicitly send a magic packet. Unfortunately in many networks waking on directed packet (any packet with the adapter's MAC address or IP address) or on link is likely to cause wakeup immediately after going to a low-power state. Details for any particular motherboard and network adapter are to be found in the relevant manuals; there is no general method. Knowledge of signals on the network may also be needed to prevent spurious wakening.
Unattended operation
For a machine which is normally unattended precautions need to be taken to make the Wake-on-LAN function as reliable as possible. For a machine procured to work in this way, Wake-on-LAN functionality is an important part of the purchase procedure.
Some machines do not support Wake-on-LAN after they have been disconnected from power (e.g., when power is restored after a power failure). Use of an uninterruptible power supply (UPS) will give protection against a short period without power, although the battery will discharge during a prolonged power cut.
Awakening without operator presence
If a machine that is not designed to support Wake-on-LAN is left powered down after power failure, it may be possible to set the BIOS to start it up automatically on restoration of power, so that it is never left in an unresponsive state. A typical BIOS setting is AC back function which may be on, off, or memory. On is the correct setting in this case; memory, which restores the machine to the state it was in when power was lost, may leave a machine which was hibernating in an unwakeable state.
Other problems can affect the ability to start or control the machine remotely: hardware failure of the machine or network, failure of the BIOS settings battery (the machine will halt when started before the network connection is made, displaying an error message and requiring a keypress), loss of control of the machine due to software problems (machine hang, termination of remote control or networking software, etc.), and virus infection or hard disk corruption. Therefore, the use of a reliable server-class machine with RAID drives, redundant power supplies, etc., will help to maximize availability. Additionally, a device which can switch the machine off and on again, controlled perhaps by a remote signal, can force a reboot which will clear problems due to misbehaving software.
For a machine not in constant use, energy can be conserved by putting the machine into low-power RAM standby after a short timeout period. If a connection delay of a minute or two is acceptable, the machine can timeout into hibernation, powered off with its state saved to disk.
Wake on Internet
The computer being woken does not know whether the wakeup signal comes from another machine on the same network or from anywhere else. If the magic packet can be made to reach a computer, it can originate anywhere (e.g., from the Internet). This can be achieved by a virtual private network (VPN), which makes the remote computer appear to be a member of the local area network (LAN). In the absence of a VPN, a computer connected to a router can be woken if a magic packet sent over the Internet is routed to it. This requires any firewall to be set up to allow entry of the Wake-on-LAN signal to a specified port. The port can be forwarded to the computer to be woken up; or some routers permit the packet to be broadcast to the entire LAN.[26] However, some routers do not support this as they will not forward broadcast packets.
Click here for original article.

